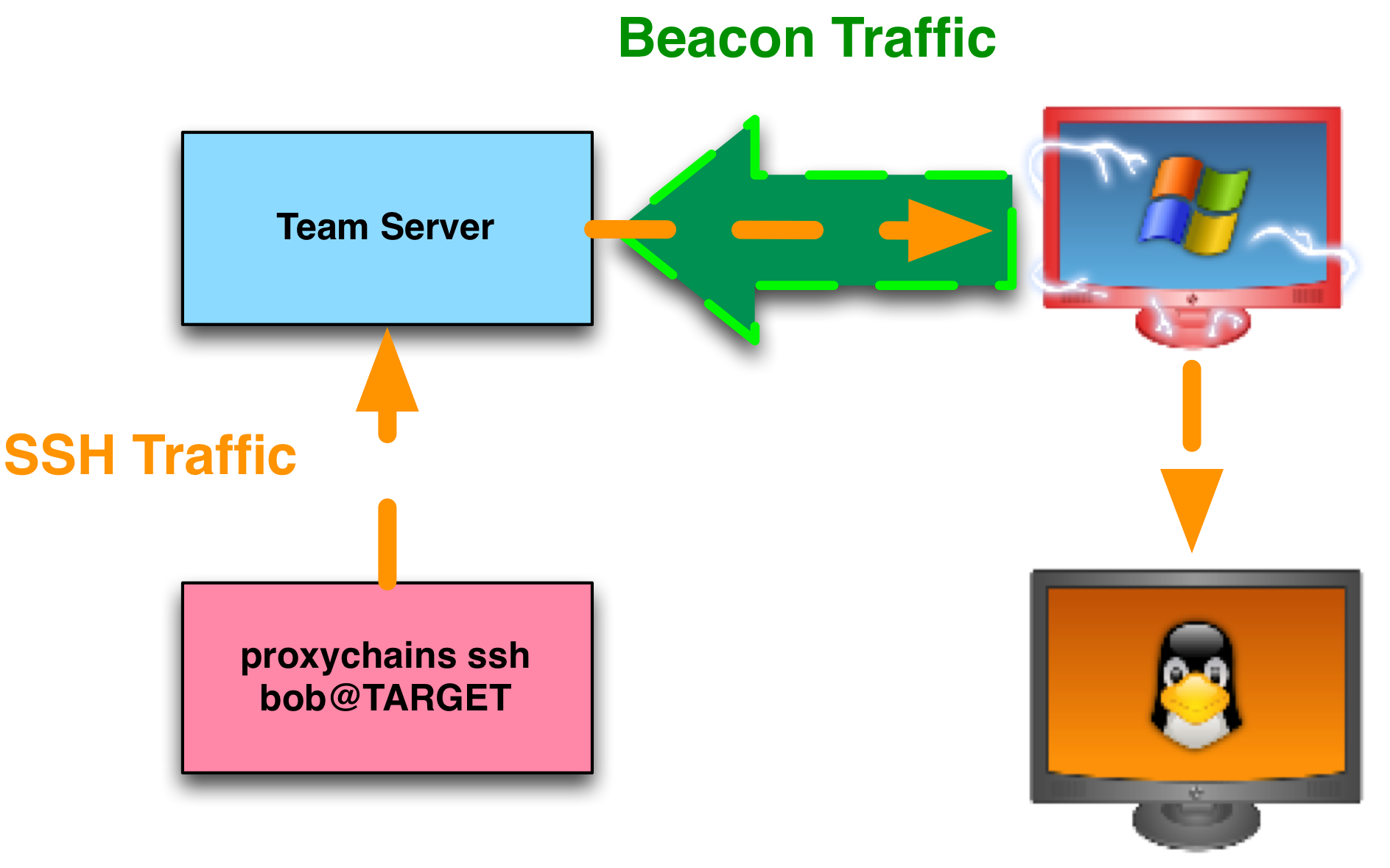
Offensive Security Guide to SSH Tunnels and Proxies | by Russel Van Tuyl | Posts By SpecterOps Team Members

Virus Bulletin on Twitter: "The DFIR Report has posted the second part of its defender's guide to Cobalt Strike, which focuses on the network traffic it produced and covers topics such as